Configuration
Why does it matter?
In a large business network it is not unusual to have lots of or hundreds of community devices. In the event you add up all your switches, routers, firewalls and various community appliances, and then you think about how many strains of configuration settings use to each one, you can see there is certainly an important investment in your networks' configuration which needs to be protected.
The most colossal challenge in hosting service configuration is not just fixing problems, however in configuring issues also. Whilst configuring, a lot of time is spent generating adjustments and adding brand new equipments, which are required to turn out to be carried out manually and takes up a great deal of time. Possessing a fanatical hosting service is not not difficult and you have a need for a person to minutely assist you with all the configuration of your system for more advantageous productivity. Server configuration management automates all of the guide work and keeps your system problems free. Because of the newest software programs equipment obtainable you can easily set your routers, switches and firewall in a fashion that they automatically notify you if any difficulty arises.
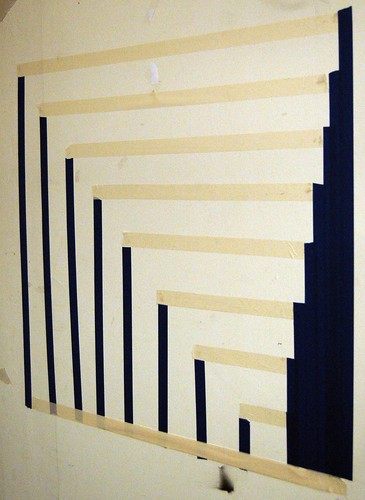
Network Configuration Backup
Create duplicate configuration of all network systems such as all of the configurable numbers that were found for every network device. The backup process might be automated for special dates and times or generated by consumer request. The backup ought to take on incremental and differential configuration settings for every network device.
Commitment to Perform
Commitment is demonstrated by the written organizational plan for computer software configuration administration (SCM). This plan are required to state who's responsible for SCM, how SCM is carried out via every project life cycle, a source library instrument is used, and that baselines are established and frequently audited. The policy are likely to be as much as the organization to outline unless it really is defined within the scope for your project.
The most important guideline for applying is to begin CM early within the project life cycle. The task supervisor should investigate the conceivable fluidity of the venture early on, and build the appropriately scaled configuration management system during the venture planning instead of half-way via the execution. When inquired what type they would do differently now time, most teams say they might trigger their vary management activities earlier of their next project, rather than viewing it as an add-on or afterthought (.
All the above might be experienced as simply varying classes of an Issue.
So what's Configuration Management? Well it truly is quite simply an
Discover more about configuration management here.
Odelia Paul is todays Configuration Management commentator who also discloses information student discount software,data recovery renton,compare newegg on their own site.